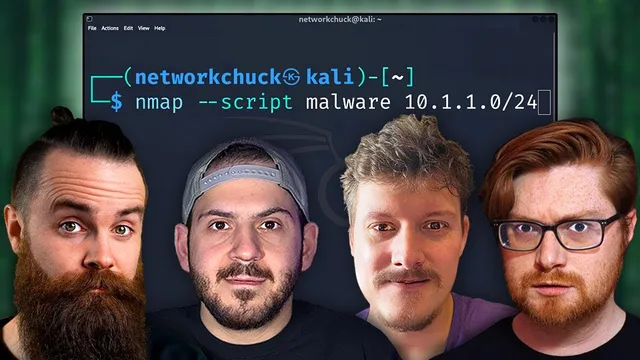
60 Hacking Commands You NEED to Know
Based on NetworkChuck's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Use ping and Hping3 not only to check reachability but to probe firewall behavior by changing packet size and generating controlled floods.
Briefing
The core takeaway is that practical “hacking commands” aren’t just about exploitation—they’re a toolkit for reconnaissance, traffic shaping, evasion, packet capture, and remote access. The walkthrough strings together dozens of command-line utilities (mostly Linux-focused) that help identify live hosts, test firewall behavior, map networks, enumerate web and WordPress surfaces, and then pivot into remote shells and tunneling when direct access is blocked.
It starts with basic connectivity testing using ping, then quickly turns ping into a firewall-testing instrument. Packet size changes (e.g., using a dash S size flag) and high-volume flooding (combining large packets with a flood switch) are used to stress targets and observe how defenses react. To make the effects visible in real time, the session introduces IF top for monitoring bandwidth during floods, and then escalates to Hping3 for more granular control: flooding specific ports, adding verbose output, and performing trace-style probing. A key pivot is using trace and port-specific behavior—running trace route against web ports (like 80) so the probing resembles legitimate traffic patterns.
When filtering blocks normal traffic, the transcript highlights tunneling as a workaround. P-tunnel is used to carry TCP over ICMP echo traffic, effectively wrapping SSH inside ICMP packets. TCP dump then becomes the live “truth serum,” capturing ICMP packets so the ICMP-based tunnel can be confirmed while an SSH session is established. The message is clear: if a firewall blocks a protocol, tunneling can repackage it into something the firewall allows.
From there, reconnaissance tools take center stage. Nmap is used for host discovery, service enumeration, OS detection, and vulnerability scanning via scripts (including malware-related checks). The walkthrough also emphasizes stealth tactics: avoiding ping probes, fragmenting packets, spoofing source ports to look like DNS, and using decoys to obscure the scanner’s origin. For scale, Masscan is introduced as a faster alternative for large network sweeps, with rate controls and randomized host ordering.
The command set then broadens beyond “classic hacking” into web and workflow utilities. Whois and WhatWeb provide domain and technology intelligence (including identifying Shopify). Curl is positioned as an API recon workhorse, showing how to inspect headers, follow redirects, and send custom authentication headers.
For web exploitation surface mapping, the transcript uses Nikto for vulnerability scanning, GoBuster for directory and file enumeration, and DNS-focused enumeration via SecLists and wordlists (including a Jason Haddock DNS list). It also covers WPScan for WordPress-specific enumeration and vulnerability checks, noting that an API token is required for richer results.
Finally, the transcript moves into persistence and remote control. It demonstrates a Bash setuid-based backdoor concept (via chmod with the setuid bit on /bin/bash) to regain root access later—framed as a “favorite” command but clearly a high-risk technique. It also returns to packet analysis with TShark (Thar) for filtering HTTP requests, extracting endpoints, and following TCP streams. Operationally, Tmux helps manage multiple sessions. Remote access is handled with SSH, including running single commands remotely and creating a SOCKS proxy to route browser traffic through another region.
The closing sections cover Netcat for reverse shells and simple chat-style connectivity, reinforcing the theme: command-line mastery spans discovery, evasion, observation, and control—often all in the same workflow.
Cornell Notes
The transcript assembles a command-line “playbook” for offensive security workflows: recon, traffic manipulation, evasion, packet capture, and remote access. It begins with ping and Hping3 to test reachability and firewall behavior, then shows how tunneling (P-tunnel over ICMP) can carry SSH when direct traffic is blocked, with TCP dump used to verify the tunnel in real time. Nmap and Masscan handle host/service discovery and vulnerability checks at different scales, while web-focused tools (Whois, WhatWeb, Nikto, GoBuster, WPScan) map web and WordPress attack surfaces. The later sections add operational tooling (Tmux, TShark) and control mechanisms (SSH SOCKS proxy, Netcat reverse shells), culminating in persistence concepts using setuid Bash.
How does the transcript turn basic ping into a firewall-testing tool rather than just a connectivity check?
What’s the purpose of using Hping3 and port-specific probing in the workflow?
Why tunnel TCP over ICMP, and how is the SSH tunnel verified?
Which Nmap options are used for stealth and for different types of discovery?
How do GoBuster and wordlists fit into web and DNS enumeration?
What roles do TShark (Thar), Tmux, and SSH SOCKS proxy play in the operational workflow?
Review Questions
- Which command(s) in the transcript demonstrate packet-size manipulation and flooding, and what firewall behavior is being tested?
- How does the workflow confirm that SSH is actually being carried over ICMP when using P-tunnel?
- What combination of Nmap options is used to both identify services/OS and reduce detectability (e.g., probes, fragmentation, source port, decoys)?
Key Points
- 1
Use ping and Hping3 not only to check reachability but to probe firewall behavior by changing packet size and generating controlled floods.
- 2
When direct TCP traffic is blocked, tunnel TCP over ICMP with P-tunnel and verify the encapsulation using TCP dump filtered to ICMP.
- 3
Rely on Nmap for host discovery, service enumeration, OS detection, and script-based vulnerability/malware checks; scale out with Masscan for faster sweeps.
- 4
Apply stealth tactics in scanning—skip ping probes, fragment packets, spoof source ports, and use decoys—to reduce attribution and detection risk.
- 5
For web recon, combine Whois and WhatWeb for domain intelligence with Nikto, GoBuster, and WPScan for vulnerability and content enumeration.
- 6
Use TShark for targeted packet filtering and stream analysis, and Tmux to keep multiple recon/attack sessions organized.
- 7
Netcat and SSH provide practical control paths: Netcat for reverse shells and SSH for remote command execution and SOCKS proxy routing.