Access ANY Network (remotely)
Based on NetworkChuck's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Twin Gate enables remote access to an internal network by deploying a connector device inside that LAN, rather than relying on traditional VPN routing.
Briefing
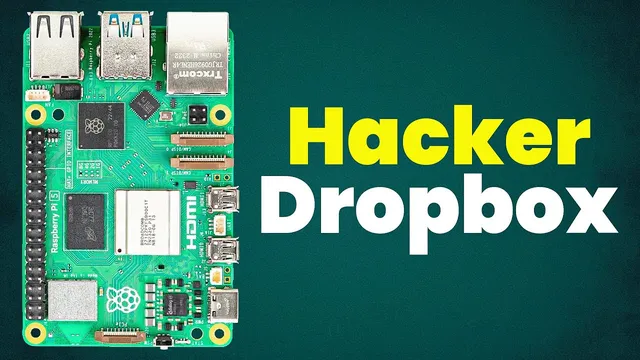
A small “connector” device can be plugged into any local network—home, church, or someone else’s office—and then accessed remotely with granular permissions, without setting up a traditional VPN. The core pitch is that Twin Gate’s zero-trust network access (ZTNA) turns a Raspberry Pi–style box into a controllable gateway: once it’s deployed inside a network, remote users can discover the connector’s IPs, create access resources, and then SSH, scan, or monitor internal machines based on tightly scoped policies.
The motivation is practical. For the church’s unofficial IT needs, troubleshooting networking issues remotely is often a time sink, especially when the “help desk” is constantly getting pulled into parents’, friends’, and family members’ problems. Full network access would make support faster and more reliable. A second use case is ethical penetration testing: dropping the device into an unknown network can reveal what it’s connected to and enable remote interaction with internal hosts—useful for authorized testing and diagnostics.
Setup starts with Twin Gate account creation and building a cloud-managed network. The workflow then defines an on-premise “remote network” (named for the church) and deploys a connector onto the target LAN. The connector can run on a Raspberry Pi (4/5/3/0 mentioned), but the approach is flexible: any supported device can host the connector software. Before deployment, the Pi’s SD card is reflashed using Raspberry Pi Imager, with pre-baked settings like device name and Wi‑Fi credentials so the box can join the target network after it’s shipped or carried in.
After powering up, Twin Gate registers the connector and shows its status in the admin console. From there, the “hard part” becomes policy and resource creation. If the internal IP range is unknown, a Python script using Twin Gate’s API can auto-discover the connector’s public and private IPs and create resources automatically. The script requires an API URL and an API key generated in Twin Gate, then uses Python modules (including requests) to query the controller and provision resources tied to the connector’s private IP.
Once a Twin Gate client is installed on a remote machine, access is granted through least-privilege defaults: resources start with no one allowed until access is explicitly added to a group (like “everyone”). The result is immediate, practical control—SSH into the connector, install tools like Nmap, and scan the internal /24 network. Twin Gate also supports tightening access further by restricting ports (e.g., only allowing SSH on port 22) and creating aliases that behave like DNS entries.
Beyond interactive support and scanning, the system adds operational security and monitoring. Access can be limited by device trust, encryption/firewall requirements, expiration windows, and auto-locking. It also supports “services” for application-style access: a service account can be configured to let a monitoring tool (example given: Uptime Kuma) reach only specific resources (like a printer) without opening firewall rules. The overall takeaway is that remote network access becomes plug-in-and-go, cloud-orchestrated, and permissioned down to ports, devices, and time windows—positioned as “not VPN,” but functionally better suited for controlled remote administration and authorized testing.
Cornell Notes
Twin Gate provides zero-trust network access that lets a user remotely reach an internal network through a small “connector” device placed inside that LAN. After deploying the connector (often a Raspberry Pi), Twin Gate registers it in the cloud and allows creation of access “resources” tied to the connector’s private IP. If the internal network details are unknown, an API-driven Python script can auto-discover the connector IPs and provision resources automatically. Access works through a Twin Gate client and least-privilege defaults, so permissions must be explicitly granted (e.g., to an “everyone” group). Policies can be tightened with port restrictions, device trust requirements, expiration, and even service accounts for monitoring tools like Uptime Kuma.
What problem does the “connector” approach solve compared with traditional VPN access?
How does the workflow handle unknown internal IP ranges when the connector is first plugged in?
What does “least privilege” look like in practice during access setup?
How can access be constrained beyond “can connect” to “can only do X”?
How does the system support monitoring without opening firewall rules?
Why pre-configure Wi‑Fi on the Raspberry Pi before deployment?
Review Questions
- When would you choose manual resource creation in Twin Gate instead of using the API-based Python discovery script?
- Describe how port restrictions and aliases change what a remote user can do after the connector is deployed.
- What security controls (device trust, expiration, auto-lock, encryption/firewall requirements) can be applied to a resource, and why do they matter?
Key Points
- 1
Twin Gate enables remote access to an internal network by deploying a connector device inside that LAN, rather than relying on traditional VPN routing.
- 2
A Raspberry Pi can be reflashed and pre-configured (including Wi‑Fi credentials) so it automatically joins the target network after placement.
- 3
Twin Gate admin setup defines an on-premise “remote network,” then deploys connectors that appear as connected relays/controllers in the console.
- 4
An API-driven Python script can auto-discover the connector’s public/private IPs and provision access resources when internal addressing is unknown.
- 5
Access follows least-privilege defaults: resources require explicit permission grants to groups before any remote client can connect.
- 6
Security can be tightened with port restrictions, device trust policies, expiration windows, and auto-locking to limit exposure over time.
- 7
Service accounts allow applications (e.g., Uptime Kuma) to monitor specific internal resources without opening firewall rules broadly.