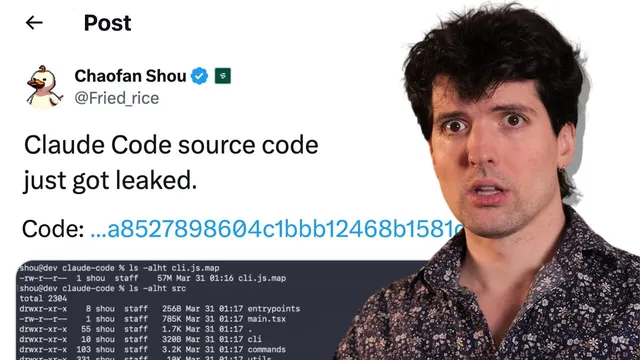
BREAKING: Claude Code source leaked
Based on Theo - t3․gg's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Claude Code’s distributed npm package included source maps that contained enough original source material to reconstruct major parts of its TypeScript codebase.
Briefing
Claude Code’s bundled JavaScript shipped with source maps that effectively exposed large portions of its underlying TypeScript source—triggering a wave of takedowns, speculation, and rapid community reverse-engineering. The leak matters because source maps are designed to map minified production code back to the original code for debugging; when they include the original sources, they turn “obscured” software into something far more inspectable. In this case, the source maps appear to have contained enough material to reconstruct major parts of Claude Code’s codebase, including unreleased features and internal mechanisms.
The chain of events starts with how modern web/Node tooling works: browsers and JavaScript runtimes can’t execute TypeScript directly, so build pipelines transform TypeScript into minified or obfuscated JavaScript. That transformation makes debugging difficult, so developers generate source maps—files that link positions in the shipped code back to the original source. Error monitoring services like Sentry can use those maps to produce readable stack traces without exposing the original code to end users. But for Claude Code, the source maps weren’t kept hidden; the npm package appears to have included a source map folder containing the original source content. The result is that anyone downloading the package could inspect the “real” code behind the obfuscated CLI.
Anthropic has reportedly sent extensive DMCA requests in response to earlier leaks of Claude Code source via the same mechanism, and this incident follows that pattern. The transcript argues the most likely cause wasn’t a deliberate “intentional leak,” but a packaging mistake—possibly tied to efforts to improve production logging after rate-limit issues surged. A key clue is that the leak included references to an internal dependency (Claude Agent SDK 0.2.88) that later disappeared when the release was pulled, breaking local installs for the investigator and forcing downgrades.
A set of conspiracy theories then gets addressed. One claims the leak was intentional; the counterpoint offered is that the original downloadable artifact was taken down quickly and that Anthropic’s history of DMCA enforcement makes “controlled release” unlikely. Another theory blames bun’s web hosting behavior (bun serve sometimes exposes source maps), but the transcript says Claude Code doesn’t use bunserve, and an employee associated with bun reportedly pointed to that mismatch. A further theory suggests competitors can now improve their own harnesses; the transcript counters that Claude Code’s harness performance is comparatively weak versus alternatives and that its source isn’t a magic advantage.
Once the source was reconstructed, the most consequential takeaways are the internal feature flags and unreleased capabilities allegedly embedded in the code. Among the highlighted items are “dream mode” (background agents consolidating memories), “coordinator mode” (parallel worker agents with shared tool access), “ultra plan” and “ultra review” (long-horizon planning and automated review with billing controls), plus “auto mode” and an always-on proactive system referred to as “Chyros.” The leak also surfaces operational details like permission cascades, prompt-cache sharing strategies to reduce inference costs, and extensive feature-flag usage via GrowthBook.
Finally, the transcript pivots to what Anthropic should do next: open-source Claude Code or at least publish a credible timeline, stop aggressive DMCA campaigns against forks and non-infringing activity, and communicate transparently with the community rather than relying on legal suppression. The core message is that the “secret sauce” argument no longer holds once the code is out, and that human, engineer-led updates could turn a PR disaster into a credibility win.
Cornell Notes
Claude Code’s npm-distributed package shipped with source maps that contained the original TypeScript source, making the “secret sauce” inspectable. Source maps exist to map minified production JavaScript back to the original code for debugging, but including the original sources in the shipped maps effectively defeats obfuscation. The leak triggered DMCA takedowns and a flood of reverse-engineering, along with competing theories about intent—most of which are dismissed in favor of a packaging/logging mistake. Reconstructed code reportedly reveals feature-flagged, unreleased agentic modes (e.g., dream mode, coordinator mode, ultra plan/review) and internal engineering mechanisms like prompt-cache sharing and GrowthBook feature flags. The practical implication: Anthropic’s next steps—transparency, possible open-sourcing, and less aggressive enforcement—will shape trust and developer adoption going forward.
Why do source maps become a security or IP risk when they’re included in a distributed package?
What mechanism is proposed for how the Claude Code source maps ended up shipping with the source?
How do the transcript’s rebuttals address major conspiracy theories?
What unreleased or feature-flagged capabilities are highlighted from the reconstructed source?
What internal engineering details are emphasized as key to cost and behavior?
What code-quality and operational risks does the transcript claim to find in the reconstructed source?
Review Questions
- How does the design purpose of source maps (debugging minified code) conflict with the risk of shipping original sources to end users?
- Which internal mechanisms in the transcript are presented as cost-saving (e.g., prompt-cache sharing), and why can they also increase fragility?
- What changes does the transcript argue Anthropic should make in response to the leak, and how do those changes relate to developer trust and adoption?
Key Points
- 1
Claude Code’s distributed npm package included source maps that contained enough original source material to reconstruct major parts of its TypeScript codebase.
- 2
Source maps are meant to map minified production JavaScript back to original code for debugging; when original sources are included, obfuscation fails.
- 3
The transcript frames the leak as a packaging/release error—possibly connected to production logging changes after rate-limit spikes—rather than a deliberate disclosure.
- 4
Reverse-engineered code allegedly reveals feature-flagged agentic modes such as dream mode, coordinator mode, ultra plan, and ultra review, along with an always-on proactive system called Chyros.
- 5
The reconstructed source highlights internal cost and behavior strategies like prompt-cache sharing across sub-agents and permission cascades governed by flags and settings.
- 6
The transcript warns of practical supply-chain risks when rebuilding from leaked sources, including dependency squatting on npm for workspace-tagged packages.
- 7
The recommended response emphasizes transparency (including open-sourcing or a timeline), reduced DMCA overreach, and engineer-led communication instead of legal suppression.