But how does bitcoin actually work?
Based on 3Blue1Brown's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Bitcoin treats the ledger of transactions as the system’s “money,” with transfers represented as signed entries recorded across the network.
Briefing
Bitcoin’s core trick is turning money into a shared, tamper-resistant ledger—so transfers don’t rely on a bank’s permission. The system works by combining three ingredients: digital signatures to prove who authorized a payment, a distributed ledger that everyone can keep locally, and “proof of work” that forces the network to agree on a single history by rewarding the most computationally intensive chain.
It starts with a simple problem: if anyone can write entries into a public record, how does the recipient know the sender truly approved a transaction? Digital signatures solve that. Each participant holds a secret key (SK) and a public key (PK). A signature is generated from the message plus the secret key, and anyone can verify it using the public key—without learning the secret key. The signature changes completely if even a tiny part of the message changes, making copied signatures useless for new transactions. To prevent replay attacks (reusing the same signed line multiple times), Bitcoin ties each payment to unique transaction data so every spend requires a fresh signature.
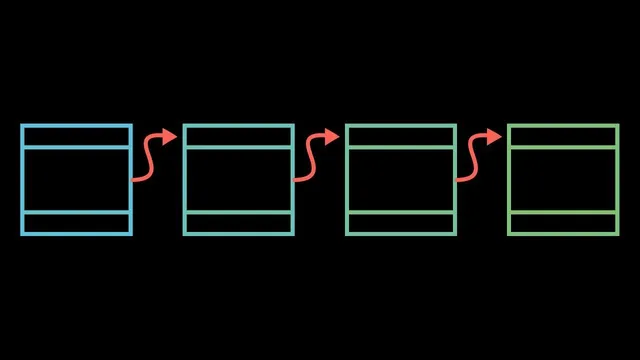
But signatures alone don’t eliminate trust. In a naive shared ledger, people would still have to settle balances honestly and in order. Bitcoin replaces that with a ledger that is replicated across the network. When Alice wants to send Bob value, the transaction is broadcast so others can record it. The hard part becomes consensus: how do nodes ensure they all store the same transactions in the same order when there’s no central authority?
Bitcoin’s answer is to make “valid history” depend on computational effort. It uses cryptographic hashing (SHA256) to compress transaction data into a fixed-length hash. Hashes behave like fingerprints: change the input slightly and the output becomes totally different. Proof of work then asks miners to find a special number (“nonce”) so that the hash of a block begins with a required number of leading zeros. Because SHA256 is effectively one-way, finding such a nonce requires brute-force guessing and verification—work that is expensive to redo.
Blocks are chained: each block header includes the previous block’s hash. That means altering an earlier block breaks the hashes of every later block, forcing miners to redo proof of work across the chain. Miners compete to extend the ledger, and the network follows the longest chain (the one with the most accumulated proof of work). If someone tries to cheat by building an alternative branch without broadcasting it widely, the rest of the network will keep extending the honest chain; without controlling roughly half the network’s mining power, the attacker’s branch becomes unlikely to catch up.
Bitcoin also defines how new coins enter the system. Miners earn a “block reward” by creating blocks, plus optional transaction fees included by users to incentivize miners to include their transactions. The block reward halves every 210,000 blocks (about four years), starting at 50 BTC and dropping to 12.5 BTC after the first halving, which caps total supply at 21 million BTC. The network targets a new block about every 10 minutes, with difficulty adjusting as more miners join. Because blocks have limited capacity (often discussed as a constraint), transaction fees can rise, since fees help determine which transactions make it into the next block.
In short: Bitcoin is not “a bank without a bank.” It’s a ruleset for maintaining a shared ledger where cryptography proves authorization, proof of work makes history costly to rewrite, and consensus emerges from which chain required the most work to build.
Cornell Notes
Bitcoin turns transfers into entries on a shared ledger that everyone can verify. Digital signatures prove that a payment was authorized by the holder of the corresponding secret key, and they prevent simple copying of signed transactions by binding signatures to unique transaction data. To resolve conflicts across many independent copies of the ledger, Bitcoin uses proof of work: miners must find a nonce so a block’s SHA256 hash starts with a target number of leading zeros. Blocks link to prior blocks via hashes, so changing history requires redoing proof of work for all following blocks. The network accepts the “longest” chain by accumulated work, and miners earn block rewards plus transaction fees, with the reward halving every 210,000 blocks.
How do digital signatures let a recipient trust that a payment was actually authorized?
Why can’t someone just reuse an old signed payment line to spend again?
What problem does proof of work solve in a distributed ledger with no central controller?
How does the hash function (SHA256) make cheating costly?
Why does the network choose the “longest” chain, and what does that mean for attacks?
How do new bitcoins enter circulation, and why do transaction fees matter?
Review Questions
- What roles do the secret key and public key play in digital signature creation and verification?
- Explain how chaining block hashes and proof of work together make rewriting past transactions computationally difficult.
- Why does Bitcoin’s consensus rule favor the chain with the most accumulated proof of work rather than a chain that arrives first?
Key Points
- 1
Bitcoin treats the ledger of transactions as the system’s “money,” with transfers represented as signed entries recorded across the network.
- 2
Digital signatures use a secret key to authorize transactions and a public key to verify them, making copied signatures unusable for new messages.
- 3
Each spend must be uniquely bound to transaction data to prevent replaying an old signed transaction multiple times.
- 4
Consensus without a central authority is achieved by proof of work: miners must find nonces so block hashes meet a difficulty target using SHA256.
- 5
Blocks link to prior blocks via hashes, so altering history forces re-mining of every subsequent block on that branch.
- 6
Nodes accept the chain with the most accumulated proof of work; attacks that try to build a competing branch become unlikely without near-total mining control.
- 7
Bitcoin’s economics combine a halving block reward (every 210,000 blocks) with transaction fees that incentivize miners to include transactions despite limited block capacity.