Hackers Rekt By Red Team - USPS SMS Scam Defeated
Based on The PrimeTime's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
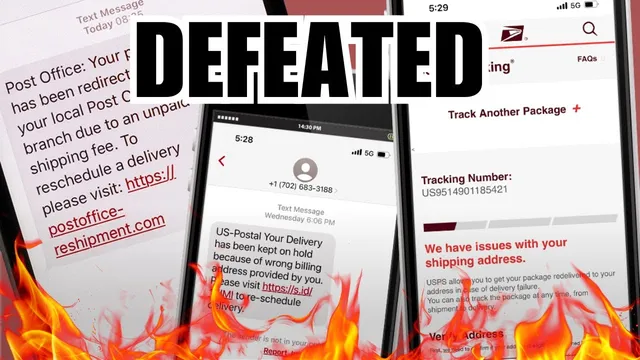
Grant Smith’s infiltration of USPS-themed smishing infrastructure helped collect evidence and victim data after his wife entered card details into a fraudulent delivery flow.
Briefing
A red-team style investigation helped dismantle a large-scale USPS smishing operation that used fake “package delivery” texts to harvest credit card details—an effort that reached hundreds of thousands of victims and exposed how attackers weaponized vulnerabilities in scam infrastructure. The key breakthrough came from security researcher Grant Smith, who infiltrated the scammers’ systems after his wife accidentally entered her card information into a fraudulent shipping flow. From there, Smith collected evidence, gathered victim data, and delivered it to U.S. authorities, enabling card protection and supporting an ongoing Postal Inspection Service investigation.
The smishing campaign, tied to a Chinese-language group dubbed the “smishing Triad,” pushed up to 100,000 scam messages per day globally. Messages impersonated the United States Postal Service, claiming a parcel needed “more details” and directing victims to a website where attackers could collect highly sensitive payment data. Smith’s work traced the operation’s infrastructure across 438,000 domains used by the scammers and revealed the scale of what victims entered: more than 50,000 email addresses (including hundreds of university accounts and about 20 military or government domains) and over 1.2 million total pieces of information. California led in entries with 141,000, reflecting how broadly the lure spread.
Technically, Smith described chaining multiple weaknesses in the scam websites. A path traversal vulnerability combined with a SQL injection—along with GraphQL-related access—allowed him to pull files from the server and read database contents. He also found that many scam sites left administrative credentials at default values, including a classic “admin/admin” pattern, which let him pull victim data faster and more automatically. Smith further identified that the scammers’ kit was sold and maintained through Telegram, where a subscription model (reported as $200 per month) enabled buyers to spin up customized fake delivery sites.
The investigation didn’t just map the threat; it helped blunt immediate harm. Smith’s wife canceled her card quickly, but attackers still attempted transactions afterward, including attempts to use the card with services like Uber. Smith’s findings were shared with a bank that had contacted him after his initial reporting, and he also provided information to the FBI and the United States Postal Inspection Service. Michael Martell, a national public information officer at USPIS, said the information is being used as part of an ongoing investigation and that agencies cannot comment on specific details.
The broader implication is that smishing is increasingly effective because it bypasses the “hover and inspect” safety habits people use against email links. Instead, SMS notifications create urgency and immediacy, driving victims to interact with fraudulent pages. Smith’s presentation at DEF CON highlighted not only the operational scale of the “smishing Triad,” but also the uncomfortable legal gray zone around “hacking back”—even when the target is foreign-based criminal infrastructure and the end goal is evidence collection and victim protection.
Cornell Notes
Grant Smith investigated a large USPS “smishing” campaign after his wife entered credit card details into a fake package-delivery flow. By infiltrating the scammers’ systems, he collected evidence and victim data tied to 438,000 scam domains and more than 1.2 million total data entries. The operation, linked to a Chinese-language group dubbed the “smishing Triad,” sent 50,000–100,000 texts per day and sold a customizable smishing kit via Telegram. Smith attributed access to weaknesses such as path traversal and SQL injection (with GraphQL-related access) and noted many sites used default admin credentials. His findings supported bank protections and an ongoing U.S. Postal Inspection Service investigation.
How did the USPS smishing lure work, and what made it effective?
What did Smith find about the scale of the scam infrastructure and victim data?
Which technical weaknesses enabled Smith to access the scam websites and databases?
How was the “smishing Triad” operation organized and monetized?
What happened after Smith shared findings with authorities and financial institutions?
Review Questions
- What combination of vulnerabilities did Smith describe using to access scam infrastructure, and why did default admin credentials matter?
- How do smishing messages differ from email phishing in terms of user behavior and safety checks?
- What evidence suggests the “smishing Triad” was a kit-based operation rather than a single-off scam?
Key Points
- 1
Grant Smith’s infiltration of USPS-themed smishing infrastructure helped collect evidence and victim data after his wife entered card details into a fraudulent delivery flow.
- 2
The “smishing Triad” campaign pushed tens of thousands of SMS messages daily and used hundreds of thousands of domains to route victims to data-harvesting pages.
- 3
Smith reported more than 1.2 million total data entries, including over 50,000 email addresses and sensitive payment information such as security codes and dates of birth.
- 4
Technical access relied on weaknesses including path traversal and SQL injection, with GraphQL-related access enabling database and server data retrieval.
- 5
Many scam sites left administrative credentials at default values, allowing faster automated extraction of victim records.
- 6
The operation’s kit was sold and customized via Telegram on a subscription model, enabling other actors to run impersonation campaigns.
- 7
Smith’s findings were shared with financial institutions and U.S. authorities, including the FBI and the United States Postal Inspection Service, supporting an ongoing investigation and fraud mitigation.