Hybrid Oracle Data Guard without Transparent Data Encryption (TDE) License
Based on Oracle Database Product Management's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Oracle Database 19.16 enables hybrid Data Guard encryption compliance without an on-prem TDE license by using TABLESPACE_ENCRYPTION to shift encryption/decryption responsibilities to the standby side.
Briefing
Hybrid Oracle Data Guard can be made to comply with OCI encryption requirements even when the on-premises primary database has no Transparent Data Encryption (TDE) license—by shifting decryption/encryption behavior to the standby side using a new static initialization parameter. The core issue is straightforward: if an unencrypted on-prem primary ships redo/data to an OCI standby over an encrypted channel, Oracle’s mandate still requires that data be encrypted before it’s written to the standby. Without special handling, a role switch would force manual intervention—decrypting incoming data on the standby and then re-encrypting it, which effectively demands a fully functional TDE setup (including licensing) on the primary.
Oracle Database 19.16 addresses this gap. With the right configuration, the primary can remain unencrypted while still participating in a complete TDE environment: the primary sends cleartext over an encrypted transport, but the standby decrypts before writing. After a Data Guard role switch, the newly promoted primary can immediately access the required encryption keys because the standby has an auto-open wallet and the master key is already present. The mechanism relies on introducing the static initialization parameter TABLESPACE_ENCRYPTION with a “decrypt only” setting on the side that lacks a TDE license, and complementary settings on the other side so that tablespaces end up encrypted with AES256 where required.
A live walkthrough demonstrates the operational steps. First, both primary (on-prem) and standby (OCI) create the directory structure needed for TDE wallet storage and set WALLET_ROOT, a static parameter that requires a restart. Next, the configuration diverges: the on-prem primary sets TABLESPACE_ENCRYPTION to decrypt-only behavior (and ensures the default algorithm is AES256 rather than the default AES128), while the OCI standby sets the parameter to auto-enable so tablespaces are encrypted as they are created/replicated. The demo then creates a password-protected auto-open wallet on the primary, sets the first master encryption key for the container database and all PDBs, and copies the wallet to the standby.
To prove encryption is actually happening, the demo creates an encrypted tablespace on the primary, inserts and queries data, and verifies from the root container that the corresponding tablespace is encrypted on the standby. While the standby’s MRP is paused briefly, remaining tablespaces are encrypted—only the ones targeted for user/system coverage—without primary downtime. After restarting MRP, queries confirm which tablespaces are encrypted on each side.
Finally, a Data Guard broker role switch promotes the standby. The new primary can read encrypted data immediately because the auto-open wallet is in place and the master key is available. The demo deletes the original test tablespace, creates a new one, and shows that it becomes encrypted on the new primary (auto-enable behavior) while the old primary remains unencrypted.
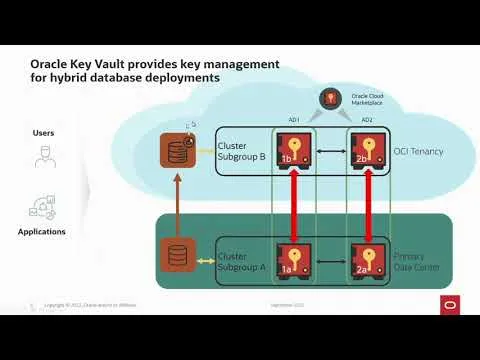
The closing guidance broadens the message: even when only a few databases use hybrid deployment, key management still matters. Oracle Key Vault (OKV) is positioned as a way to centralize wallets and synchronize encryption keys across an OKV cluster, reducing wallet-copy overhead and avoiding key material on database hosts. The result is a cleaner operational model for Data Guard encryption in mixed licensing scenarios.
Cornell Notes
Hybrid Oracle Data Guard can satisfy OCI’s encryption mandate without an on-prem TDE license by using Oracle Database 19.16’s TABLESPACE_ENCRYPTION static parameter to control where decryption/encryption happens. The on-prem primary can send cleartext over an encrypted channel, while the OCI standby encrypts data before writing it, so tablespaces end up encrypted with AES256. A complete TDE setup is still required for key availability, but licensing can be avoided on the primary by configuring “decrypt only” behavior there and “auto enable” on the standby. An auto-open wallet and master key are created on the primary, copied to the standby, and then role switches work immediately because the promoted primary can access keys right after restart. The demo validates encryption status before and after a broker-driven switchover.
Why does an unencrypted on-prem primary create a problem for OCI Data Guard encryption compliance?
What change in Oracle Database 19.16 makes the hybrid approach workable?
What is the role of WALLET_ROOT and why does it require a restart?
How does the demo ensure the standby encrypts tablespaces with AES256?
How does the system keep working after a Data Guard role switch?
Why does key management remain important even when the primary isn’t encrypted?
Review Questions
- What specific behavior does TABLESPACE_ENCRYPTION enable on the unlicensed primary versus the OCI standby, and how does that affect what gets encrypted before writing?
- During the walkthrough, which steps ensure the wallet and master key are available immediately after a broker-driven switchover?
- How does the demo verify encryption status on both sides, and what changes after the role switch?
Key Points
- 1
Oracle Database 19.16 enables hybrid Data Guard encryption compliance without an on-prem TDE license by using TABLESPACE_ENCRYPTION to shift encryption/decryption responsibilities to the standby side.
- 2
Set WALLET_ROOT to point to TDE wallet directories; because it’s static, both primary and standby require restarts after changing it.
- 3
On the unlicensed primary, configure TABLESPACE_ENCRYPTION for decrypt-only behavior and set the default algorithm to AES256 before creating the first key.
- 4
On the OCI standby, configure TABLESPACE_ENCRYPTION to auto-enable so tablespaces are encrypted with AES256 as they are written.
- 5
Create an auto-open, password-protected wallet on the primary, set the first master key for the CDB and all PDBs, and copy the wallet to the standby so role switches work immediately.
- 6
Encrypt targeted tablespaces (e.g., user and selected system-related tablespaces) without primary downtime by coordinating with MRP.
- 7
For broader operations, Oracle Key Vault can centralize wallet/key management and synchronize keys across an OKV cluster to reduce wallet-copy overhead and key footprint on database machines.