North Korean Hacker Infiltrates US Company
Based on The PrimeTime's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
The incident was not a data breach: no illegal access was gained and no data was lost, compromised, or exfiltrated.
Briefing
A North Korean “fake IT worker” was hired as a principal software engineer at a U.S. company, then triggered rapid detection and containment after malware was loaded onto a company MacBook almost immediately. No illegal access was gained and no data was lost, but the incident became a high-stakes warning about how stolen identities and AI-generated impersonation can slip through standard hiring checks and turn an onboarding moment into an intrusion attempt.
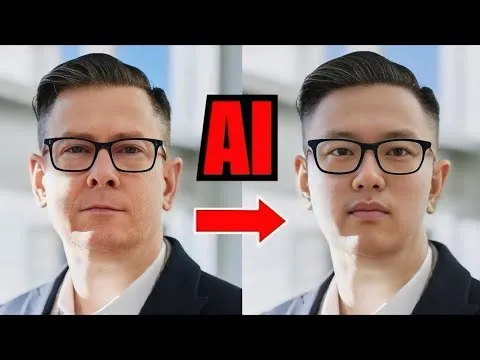
The company’s internal process looked routine on paper: a software engineer role for an internal IT/AI team, resumes reviewed, interviews conducted, background checks and reference verification performed, and a MacBook workstation shipped to the new hire. The compromise began the moment the laptop arrived—malware loaded right away. HR also ran multiple video interviews and confirmed the person matched the photo submitted with the application. The identity used, however, was a real person’s valid U.S.-based identity that had been stolen, and the profile photo was AI-enhanced, making the deception harder to spot.
Endpoint detection and response (EDR) software flagged the activity and alerted the security operations center (SOC). SOC then contacted the new hire, and the situation deteriorated quickly. The company shared collected data with Mandant, a global security firm, and coordinated with the FBI. Investigators determined the suspicious activity aligned with a North Korean state-linked insider threat attempt.
On July 15, 2024, suspicious actions were detected on the user account starting at 9:55 p.m. Eastern Standard Time. The new hire—identified in the report as “employer ID xxxxx” and referred to as “Quadruple X” in the narrative—claimed he was troubleshooting a router speed issue using a router guide, attributing the anomalies to that work. But the attacker’s behavior went beyond troubleshooting: session history was manipulated, files were transferred, potentially harmful files were moved, and unauthorized software was executed.
Containment happened within minutes. SOC contained the device less than 25 minutes after the initial outreach, after the user became unresponsive around 10:20 p.m. The suspected operational method relied on an “IT mule” setup: the attacker requested the workstation be shipped to an address controlled by the scheme, then used a VPN to connect from the real physical location—described as North Korea or nearby territory—while appearing to work during U.S. daytime.
The incident report emphasizes that the case was not a data breach notification; it was an organizational learning moment. It also highlights practical red flags and controls: strengthen identity verification beyond email and references, add physical-location checks, improve resume and career-consistency screening, require video-based validation that goes deeper than matching a photo, and tighten monitoring and authentication for remote access. The overall takeaway is blunt: even with background checks and interviews, advanced actors can exploit onboarding workflows—so continuous security monitoring and stronger hiring-security coordination are essential.
Cornell Notes
A North Korean-linked actor used a stolen, valid U.S. identity and an AI-enhanced photo to get hired as a principal software engineer. Malware loaded immediately when the company-issued MacBook arrived, and endpoint detection (EDR) alerted the SOC. Investigators coordinated with Mandant and the FBI, and determined the activity was consistent with an insider threat attempt; no data was lost or exfiltrated. Containment occurred in under 25 minutes after suspicious account activity was detected. The case underscores that onboarding and hiring processes can be exploited, even when interviews and background checks appear to pass.
What made this incident different from a typical data breach?
How did the attacker bypass hiring safeguards?
What technical signals triggered detection and response?
What operational method was suspected behind the infiltration?
What specific improvements were recommended to reduce similar risks?
Why did the FBI involvement matter in the narrative?
Review Questions
- What combination of identity theft and AI-enhanced impersonation allowed the attacker to pass early hiring checks?
- Which behaviors on the user account went beyond “troubleshooting” and pointed to malicious intent?
- Why does shipping a company workstation to a mismatched address create an exploitable gap during onboarding?
Key Points
- 1
The incident was not a data breach: no illegal access was gained and no data was lost, compromised, or exfiltrated.
- 2
A stolen but valid U.S.-based identity plus an AI-enhanced photo helped the attacker pass interviews and background checks.
- 3
Malware loaded immediately when the company-issued MacBook arrived, triggering EDR detection.
- 4
SOC detected suspicious account activity and contained the device in under 25 minutes after outreach.
- 5
The suspected scheme used an IT-mule shipping address and VPN access to make work appear to originate from the U.S. daytime.
- 6
Recommended defenses include stronger identity verification, deeper resume and reference scrutiny, physical-location checks, and tighter access controls and authentication.
- 7
Continuous monitoring and HR–security coordination are critical because onboarding workflows can be exploited even when checks “clear.”