Put your website on the Dark Web
Based on NetworkChuck's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Onion Share can host a website, run anonymous chat, and share files over Tor using temporary onion addresses.
Briefing
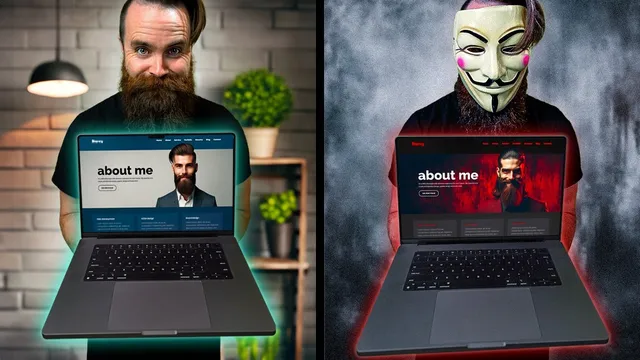
A practical, step-by-step setup shows how to host a website, run an anonymous chat, and share files on Tor using Onion Share—then escalates to a more permanent “Dark Web Supreme” setup with a custom onion address. The core takeaway is that Tor’s onion routing can be used to publish content under an onion domain without exposing the server’s IP address, while Onion Share provides a quick, ephemeral way to go live and take the service down instantly.
The walkthrough splits into two tracks. “Dark Web Light” uses Onion Share, a tool installable across platforms, to connect to the Tor network and publish a local folder as a Tor-accessible site. The process is intentionally simple: install Onion Share, connect to Tor, drag a “website” folder into the share interface, and start sharing. By default, the site is not public; Onion Share generates a short-lived onion address plus a secret key. Visitors using a Tor browser must supply that key to unlock access. Once sharing stops, the onion service disappears—refreshing from the client side no longer works—making the setup feel more like a controlled demo than a long-running service.
Onion Share also supports anonymous chat sessions and file transfer. For chat, the method can run via a GUI or a CLI workflow on Linux. A Tor browser can open the generated chat address, and messages appear to the other side without requiring direct network visibility between participants. For file sharing, Onion Share generates a one-time onion address for a specific file; downloads occur over Tor, and the author notes that this works without router port forwarding.
The “Dark Web Supreme” section moves from ephemeral sharing to a durable hosting model. It starts with a standard web server: Nginx is installed on an Ubuntu (or Debian-based) Linux machine, a portfolio site is copied into Nginx’s web root, and the page is verified over HTTP on the local network. Then Tor is installed from Tor’s Debian repositories, and Tor’s configuration is edited to enable a hidden service that forwards port 80 to the local web server. After restarting Tor, the onion address and keys are located under Tor’s hidden service directory, and the portfolio site is confirmed accessible from a Tor browser.
The most distinctive part is custom “vanity” onion domains. Instead of accepting a random onion hostname, the guide installs a tool (named “MKP2240”) that brute-forces onion addresses until the beginning matches a chosen keyword. The tradeoff is computational cost: shorter vanity strings are found quickly, while longer phrases can take much longer. Once the generated keys are copied into Tor’s hidden service directory and Tor is restarted, the service comes up under the vanity onion address.
Overall, the workflow turns Tor from a concept into a repeatable deployment pattern: quick publishing with Onion Share, then full control with Nginx + Tor hidden services, plus optional vanity onion hostnames for memorability and branding.
Cornell Notes
The guide shows two ways to publish content on Tor. “Dark Web Light” uses Onion Share to host a website, run anonymous chat, and share files via temporary onion addresses that vanish when sharing stops. Visitors access the site through Tor Browser and, in the default non-public mode, must provide a secret key. “Dark Web Supreme” builds a more permanent hidden service by installing Nginx, configuring Tor to forward port 80 to the local web server, and then using Tor’s generated onion hostname and keys. It also demonstrates vanity onion addresses by brute-forcing onion hostnames to match a chosen keyword, with longer strings requiring more CPU time.
How does Onion Share keep a hosted site from being permanently exposed once sharing ends?
What’s the practical difference between Onion Share’s “public” mode and the default keyed mode?
Why does the guide emphasize Tor’s “six onion relays” and layered encryption?
How does “Dark Web Supreme” differ from “Dark Web Light” in architecture and persistence?
What steps are required to make Nginx serve the intended portfolio site before Tor is enabled?
How does the vanity onion address feature work, and what determines how long it takes?
Review Questions
- What access control mechanism does Onion Share use in its default (non-public) website sharing mode, and what happens to access when sharing stops?
- In “Dark Web Supreme,” which two services must be running and correctly configured to serve a site over Tor, and how is the port mapping handled?
- What is the main computational tradeoff when generating a vanity onion address, and how does the chosen keyword length affect runtime?
Key Points
- 1
Onion Share can host a website, run anonymous chat, and share files over Tor using temporary onion addresses.
- 2
Default Onion Share website sharing is non-public and requires a secret key; public mode removes that key requirement.
- 3
Stopping Onion Share ends the onion service, so the site becomes inaccessible after sharing stops.
- 4
A permanent Tor hidden service setup pairs Nginx (serving content on port 80) with Tor’s torrc hidden service configuration.
- 5
Tor hidden service keys and hostnames live under Tor’s hidden service directory, and restarting Tor activates changes.
- 6
Vanity onion addresses can be generated by brute-forcing onion hostnames to match a chosen keyword, with longer strings taking more CPU time.