you need to learn Load Balancing RIGHT NOW!! (and put one in your home network!)
Based on NetworkChuck's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
Forward only TCP/443 from the router to Kemp’s VIP, then route all internal services through that single entry point.
Briefing
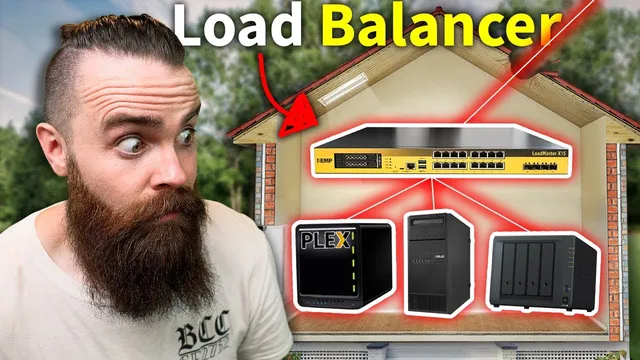
A home network can be secured and simplified by exposing only a single public entry point—HTTPS on port 443—then using a Kemp “LoadMaster” load balancer to route that traffic to many internal services (Plex, NAS, websites, Proxmox, ESXi) based on domain names and URL/host rules. The payoff is practical: fewer router “holes,” one public IP/port for everything, and HTTPS certificates that keep external access clean and browser-friendly.
The tutorial starts with what load balancing does in general: when traffic grows, multiple backend servers can share the work, but clients still need a single address to reach the service. A load balancer sits in front, accepts incoming requests, and distributes them across “real servers,” while also monitoring health so dead or unhealthy backends don’t receive traffic. That enterprise pattern is then mapped to a home lab, where the real problem isn’t CPU spikes—it’s remote access.
Without a load balancer, remote access typically means opening multiple ports on the router (for example, 443 for a website, 50001 for a Synology NAS, 32400 for Plex, and others). That approach creates multiple inbound attack surfaces and runs into a hard limitation: port 443 can only point to one internal IP, so adding more HTTPS services becomes awkward or impossible. The solution presented is to close everything except port 443 and forward that single port to the load balancer’s virtual IP (VIP). From there, the load balancer routes requests internally.
The build uses three key components. First, Kemp LoadMaster runs as a virtual appliance on a hypervisor such as VMware ESXi (with guidance that other platforms like KVM or Proxmox may require workarounds). Second, a free domain is obtained from Freenom (example used: hackwell.tk). Third, Cloudflare manages DNS and SSL. Cloudflare’s “proxy” feature hides the home’s public IP address, and its integration with Let’s Encrypt provides certificates—crucially including wildcard coverage—so subdomains like plex.hackwell.tk and nas.hackwell.tk can use valid HTTPS.
Inside Kemp, the configuration begins by creating a VIP (the single internal IP that represents the public-facing portal) and then defining “virtual services” on TCP/443. Backend services are added as real servers, including multiple NAS instances and multiple web servers. Kemp health checks verify whether each backend is actually reachable using the right protocol (HTTPS, HTTP, or even ICMP ping), and traffic is withheld from unhealthy targets.
To make routing intelligent, the setup moves beyond basic layer-3 forwarding into layer-7 content switching. Content rules inspect the Host header (e.g., requests for plex.hackwell.tk) and switch to the correct subservice, forwarding traffic to the appropriate internal port (Plex to 32400, NAS to 501, and so on). The tutorial demonstrates that Plex, Proxmox, ESXi, and a multi-server website can all be reached securely through their own subdomains while still sharing the same external port 443.
Finally, the guide highlights operational benefits: automatic failover when a backend server goes down, centralized security controls such as a built-in web application firewall option, and an enterprise-like architecture that can be replicated in real deployments. The author notes an alternative SSL approach—having Kemp handle certificates directly via Let’s Encrypt—but keeps Cloudflare as the practical choice for the home lab.
Cornell Notes
The setup uses a Kemp LoadMaster load balancer to expose home services securely through a single public HTTPS entry point (port 443). Instead of opening many router ports for Plex, NAS, Proxmox, ESXi, and websites, the router forwards only 443 to Kemp’s VIP, and Kemp routes requests to the correct internal server based on domain/Host rules (layer 7 content switching). A free domain from Freenom (example: hackwell.tk) and Cloudflare DNS/SSL provide wildcard certificates and hide the home’s public IP via proxying. Kemp health checks prevent traffic from being sent to unhealthy backends, enabling automatic failover. The result is “one port, many services,” with clean HTTPS for every subdomain.
Why does a home network typically end up opening multiple ports for remote access, and what breaks when everything needs HTTPS?
How does the Kemp LoadMaster design replace many router port forwards with one?
What role do Cloudflare and Freenom play in making the setup usable and secure?
What does “layer 7 content switching” add compared with basic load balancing?
How does Kemp avoid sending traffic to broken or offline services?
Why create a wildcard certificate, and how does it relate to subdomains?
Review Questions
- If port 443 can only map to one internal IP, how does this setup still allow multiple HTTPS services to work?
- Describe the chain of decisions from an external request to the final backend service in this architecture.
- What health-check method would you choose for a service that doesn’t have a valid HTTPS certificate, and why?
Key Points
- 1
Forward only TCP/443 from the router to Kemp’s VIP, then route all internal services through that single entry point.
- 2
Use Kemp virtual services and real servers to map one VIP/port to many backends (Plex, NAS, Proxmox, ESXi, and web servers).
- 3
Rely on Cloudflare + Freenom to get a domain and wildcard HTTPS, while Cloudflare proxying hides the home’s public IP.
- 4
Implement layer 7 content rules that match the Host header (e.g., plex.hackwell.tk) so each subdomain reaches the correct internal port.
- 5
Configure Kemp health checks per backend so unhealthy services are automatically excluded and failover can occur.
- 6
Enable strict HTTPS behavior in Cloudflare and align Kemp SSL settings so browser access stays error-free.