How I learn in Obsidian // Keeping up with tech trends
Based on Nicole van der Hoeven's video on YouTube. If you like this content, support the original creators by watching, liking and subscribing to their content.
eBPF-based monitoring is positioned as a kernel-level alternative to user-space instrumentation agents.
Briefing
eBPF is framed as an efficiency-and-operations upgrade to traditional monitoring: it shifts observability work from user-space instrumentation agents down into the kernel, where event-driven programs can listen for what matters with minimal overhead. The practical takeaway is that teams can keep the same monitoring goals—understanding what a complex system is doing—while reducing the CPU/memory tax and improving operational flexibility, especially in microservices-heavy environments.
The learning process starts with “methodology fatigue”—the difficulty of sticking to rigid note-taking rules like what counts as an “atomic” or “evergreen” note. Instead of enforcing a single system, Nicole van der Hoeven uses a workflow that prioritizes relevance and consolidation over perfect taxonomy. Notes imported into Obsidian are filtered via a tag (e.g., #TVZ, “To Verzetteln”), sorted from newest to oldest, and processed in small batches. The goal isn’t to finish every article; it’s to extract enough structure to build a coherent understanding and then iterate later.
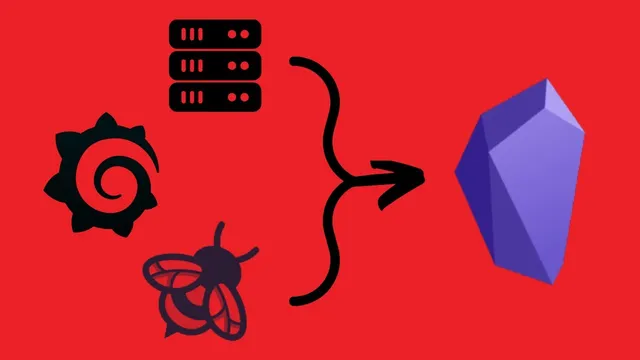
As the focus narrows to eBPF (Extended Berkeley Packet Filter), the notes emphasize a core distinction: instrumentation versus eBPF-based monitoring. Instrumentation is described as an approach where an application component in user space is paired with an instrumentation agent that collects and forwards signals. eBPF, by contrast, is positioned as operating at a lower level inside the kernel. That architectural shift matters because it reduces the need for many separate agents across components—fewer “robots” watching each node/component, more centralized kernel-level listeners.
The consolidation also highlights why eBPF is attractive in observability work. It is characterized as event-driven, meaning it can stay idle until relevant events occur rather than constantly running. Efficiency is a headline metric: Netflix is cited for judging overhead at about 1% CPU and memory, which is presented as unusually low for monitoring. Security is another selling point: eBPF is described as allowing kernel programs without granting full root access, likened to a safer “JavaScript-like” layer that constrains what kernel code can do. Finally, eBPF is tied to operational agility—continuous delivery—because eBPF programs can be shipped and updated without changing kernel code.
To make the knowledge stick, the workflow turns text into visuals. Excalidraw is used to create simplified diagrams for both instrumentation and eBPF, then Excalidraw outputs are embedded into an “advanced slides” story that narrates the monitoring pipeline from user space down to the kernel. The result is less a finished tutorial and more a living snapshot: a structured explanation that can be revised as new eBPF details arrive. The broader lesson is pragmatic—use what helps, discard what doesn’t, and treat notes as an evolving system rather than a final product.
Cornell Notes
The notes build a clear mental model of monitoring by contrasting traditional instrumentation with eBPF-based monitoring. Instrumentation relies on user-space components plus an agent that collects signals, while eBPF runs inside the kernel and listens for events at a lower level. That kernel placement enables event-driven monitoring with low overhead—Netflix is cited for roughly 1% CPU and memory impact. eBPF is also framed as safer than unrestricted kernel code (no full root access) and more operationally flexible because eBPF programs can be updated without changing kernel code. The learning workflow then turns these ideas into diagrams and a guided slide story to consolidate understanding.
What is the key architectural difference between instrumentation and eBPF monitoring?
Why does event-driven behavior matter for monitoring overhead?
What overhead claim is cited, and why is it important?
How is eBPF positioned as “more secure” than direct kernel-level access?
How does eBPF support continuous delivery in observability?
How does the note-taking workflow help consolidate learning during research?
Review Questions
- If instrumentation and eBPF both aim to improve observability, what specific layer difference (user space vs kernel) changes the monitoring design?
- Which three advantages are attributed to eBPF in the notes (efficiency, security, and delivery), and what concrete evidence or analogy is used for each?
- How does turning text into diagrams and an embedded slide story change the way the knowledge is retained or updated?
Key Points
- 1
eBPF-based monitoring is positioned as a kernel-level alternative to user-space instrumentation agents.
- 2
Event-driven kernel listeners can reduce always-on monitoring overhead.
- 3
Netflix is cited for estimating eBPF monitoring overhead at about 1% CPU and memory.
- 4
eBPF is described as safer than unrestricted kernel access because it avoids full root privileges.
- 5
eBPF programs can be updated without changing kernel code, supporting continuous delivery of monitoring logic.
- 6
A learning workflow that prioritizes relevance, partial processing, and later revision can prevent “methodology fatigue.”
- 7
Visual consolidation (diagrams and guided slide stories) helps turn research notes into a usable mental model.